Check Point Research (CPR), the Threat Intelligence arm of Check Point® Software Technologies Ltd. (NASDAQ: CHKP) and a leading provider of cyber security solutions globally, has published its new Brand Phishing Report for Q4 2021. The report highlights the brands which were most frequently imitated by criminals in their attempts to steal individuals’ personal information or payment credentials during October, November, and December.
For the first time, DHL took the number one spot in Q4, replacing Microsoft as the brand most likely to be targeted by cybercriminals in phishing scams. Twenty-three percent of all brand phishing attempts were related to the global logistics and shipping company, up from just 9% in Q3, as threat actors sought to take advantage of vulnerable online consumers during the busiest retail period of the year. Microsoft, which yet again led the rankings in Q3 by accounting for 29% of all phishing attempts, only accounted for 20% of phishing scams in Q4. FedEx also appeared in the top ten list for the first time in Q4 2021, no doubt the result of threat actors trying to target vulnerable online shoppers in the run-up to the festive season as the pandemic remained a key concern.
The Q4 report also reinforces an emerging trend from Q3, with social media seeming to solidify its position among the top three sectors imitated in phishing attempts. While Facebook has dropped out of the top ten brands most likely to be imitated, WhatsApp has moved from 6th position to 3rd, now accounting for 11% of all phishing attempts. LinkedIn has moved from 8th position to 5th, now accounting for 8% of all phishing-related attacks.
“It’s important to remember that cybercriminals are opportunists first and foremost. In their attempts to steal peoples’ personal data or deploy malware onto a user’s machine, criminal groups will often take advantage of consumer trends by imitating popular brands,” said Omer Dembinsky, Data Research Group Manager at Check Point Software. “This quarter, for the first time, we’ve seen global logistics company DHL top the rankings as the most likely brand to be imitated, presumably to capitalize on the soaring number of new and potentially vulnerable online shoppers during the years busiest retail period. Older users in particular, who are less likely to be as technologically savvy as younger generations, will be shopping online for the first time and might not know what to look for when it comes to things like delivery confirmation emails or tracking updates.”
Omer continued, “Q4 has also confirmed what many of us were expecting. That social media would continue to be heavily targeted by bad actors looking to take advantage of those leaning more heavily on channels like WhatsApp, Facebook, and LinkedIn as a result of remote working and other fallouts from the pandemic. Unfortunately, there’s only so much brands like DHL, Microsoft, and WhatsApp – which represent the top 3 most imitated brands in Q4 – can do to combat phishing attempts. It’s all too easy for the human element to overlook things like misspelled domains, typos, incorrect dates, or other suspicious details, and that’s what opens the door to further damage. We’d urge all users to be very mindful of these details when dealing with the likes of DHL in the coming months.”
In a brand phishing attack, criminals try to imitate the official website of a well-known brand by using a similar domain name or URL and web-page design to the genuine site. The link to the fake website can be sent to targeted individuals by email or text message, a user can be redirected during web browsing, or it may be triggered from a fraudulent mobile application. The fake website often contains a form intended to steal users’ credentials, payment details, or other personal information.
Top phishing brands in Q4 2021
Below are the top brands ranked by their overall appearance in brand phishing attempts:
- DHL (related to 23% of all phishing attacks globally)
- Microsoft (20%)
- WhatsApp (11%)
- Google (10%)
- LinkedIn (8%)
- Amazon (4%)
- FedEx (3%)
- Roblox (3%)
- Paypal (2%)
- Apple (2%)
PayPal Phishing Email – Account Theft Example
During November sales days, we noticed a malicious phishing email that was allegedly sent by PayPal and was trying to steal users’ credit information. The email (see Figure 1) which was sent from the spoofed address PayPal Service (service@ec2-18-156-114-201[.]eu-central-1[.]compute[.]amazonaws[.]com) was actually sent by admin_emotion_dev@emotionstudios[.]rocks, contained the socially engineered subject “[Alert] Confirm your PayPal account (Case ID #XX XXXXXXXXXX)” which could pressure the victim into clicking on the malicious link (https://serviiceds[.]ritaspizzaportsmouth[.]com/llpy/). The website redirects the user to a fraudulent PayPal login page that looks like the real site (see Figure 2) with a few minor differences in appearance. In the malicious link, the user needed to enter their PayPal account details.
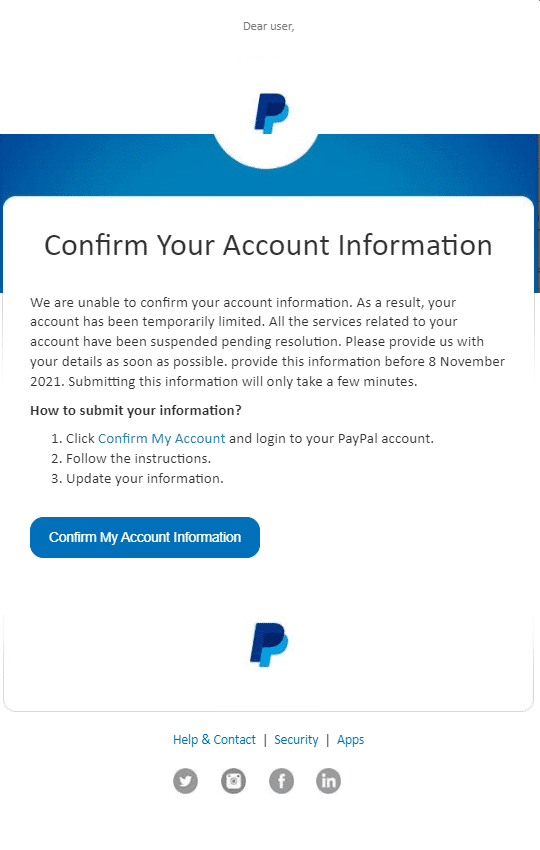
Figure 1: The malicious email which was sent with the subject
“[Alert] Confirm your PayPal account (Case ID #XX XXXXXXXXXX)”
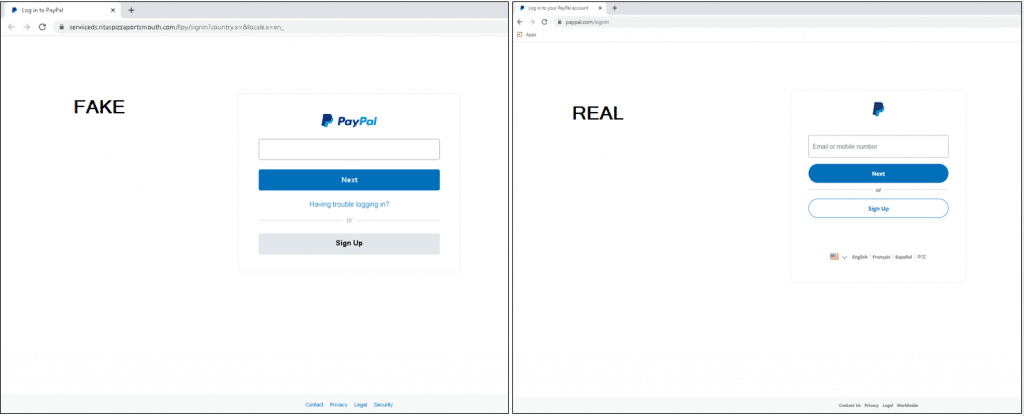
Figure 2:
Left side – fraudulent login page
Right side – real login page
Fedex Phishing Email – Malware Attached
During December, we observed a malicious phishing email that used Fedex’s branding and was trying to get the user to download SnakeKeylogger malware to their machine. The email (see Figure 1) which was sent from the spoofed address support@fedex[.]com, contained the subject “Bill of Lading-PL/CI/BL-Documents arrival”. The content is asking to download a RAR archive file “shipment docu..rar”, which contains a malicious executable file that would cause the system to be infected with SnakeKeylogger and could steal the user’s credentials information.
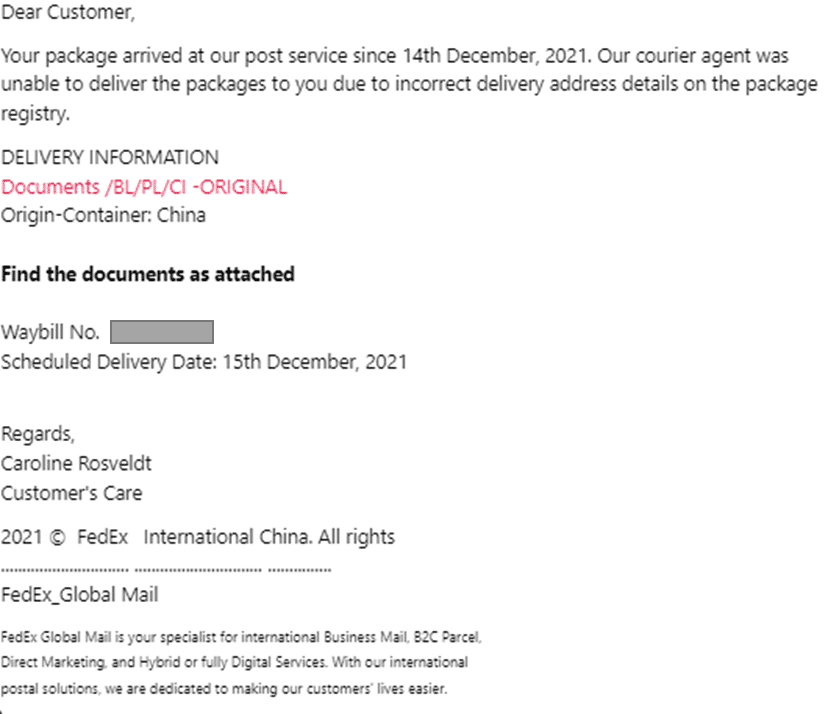
Figure 1: The malicious email which was sent with the subject
“Bill of Lading-PL/CI/BL-Documents arrival”
DHL Phishing Email – Credentials Theft Example
In this phishing email (see Figure 1), we see an attempt to steal users’ email and password. It was sent from the spoofed email address DHL Customer Support (info@emmc[.]ir), contained the subject “DHL Shipment Notification : xxxxxxxxxx “Out for delivery” for 15 Dec 21”. The attacker was trying to lure the victim to click on a malicious link (http://reg[.]chaindaohang[.]com/wp-content/uploads/2021/07/dhl/index[.]php?i=i&0=vegenat@vegenat[.]es) which redirects the user to a fraudulent DHL home page, that looks like the real website (see Figure 2). In the malicious link, the user was prompted to key-in their email and password.
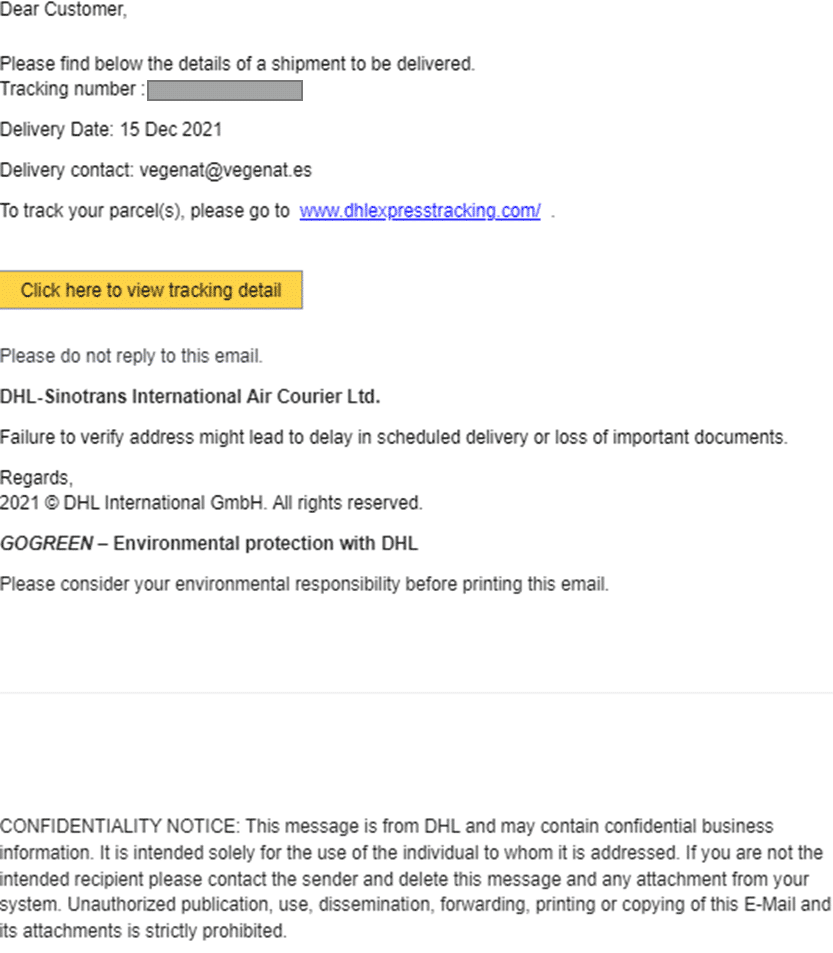
Figure 1: The malicious email which was sent with the subject
“DHL Shipment Notification : xxxxxxxxxx “Out for delivery” for 15 Dec 21”
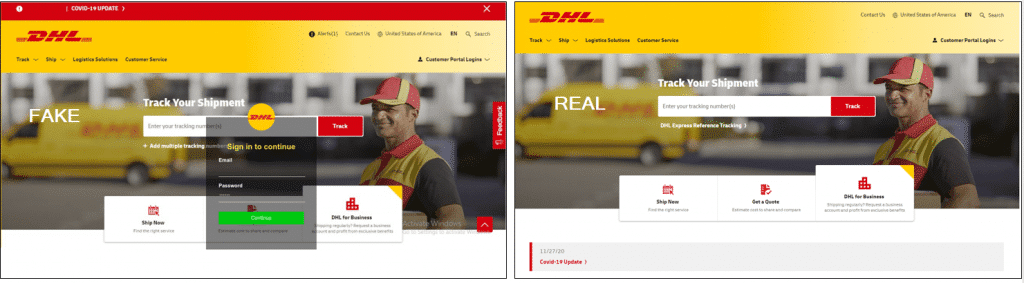
Figure 2:
Left side – fraudulent login page with credentials request
Right side – real login page
As always, we encourage users to be cautious when divulging personal data and credentials to business applications or websites, and to think twice before opening email attachments or links, especially emails that claim to be from companies such as DHL, Microsoft or Whastapp, as they are the most likely to be impersonated.
Follow Check Point Research via:
Blog: https://research.checkpoint.com/
Twitter: https://twitter.com/_cpresearch_
About Check Point Research
Check Point Research (CPR) provides leading cyber threat intelligence to Check Point Software customers and the greater intelligence community. The research team collects and analyzes global cyber-attack data stored on ThreatCloud AI to keep hackers at bay, while ensuring all Check Point solutions are updated with the latest protections. The research team consists of over 100 analysts and researchers cooperating with other security vendors, law enforcement and various CERTs.




