Check Point 的全方位功能集

Native user experience
Check Point integrates natively with database protocols, including ODBC and OLE-DB, providing users with a quick and secure connection to any database through their terminal. Any underlying security measures are undetectable.

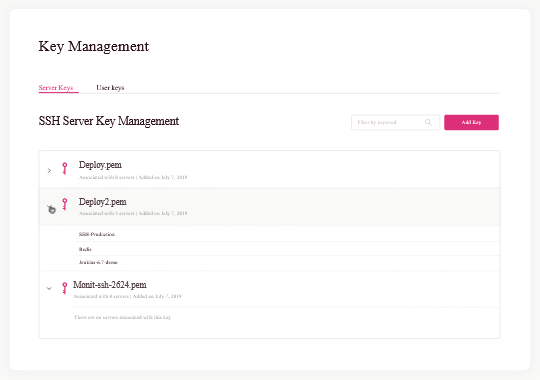
Eliminate static credentials
Static credentials pose risks to modern IT environments as they do not include user identity information, are difficult to rotate regularly and can be used by anyone who has them. Check Point’s built-in PAM solution eliminates these risks associated with users holding static keys or VPN credentials.

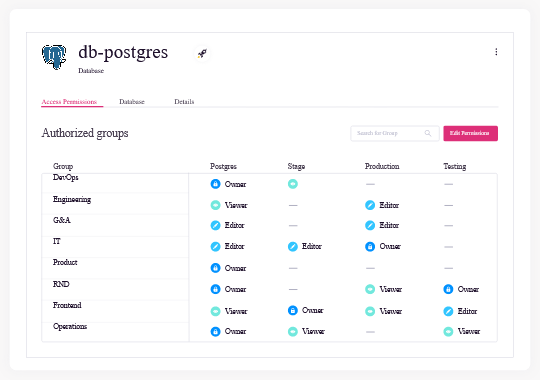
Role-Based Access Profiles
Administrators can confidently provide developers with database access based on one of three roles profiles: owner, editor, and viewer.

IDP 整合
Check Point integrates with your IDP and leverages user identities for authentication and to provide centralized role-based access management on all database servers. This includes MySQL MsSQL, Mongo, Elasticsearch.

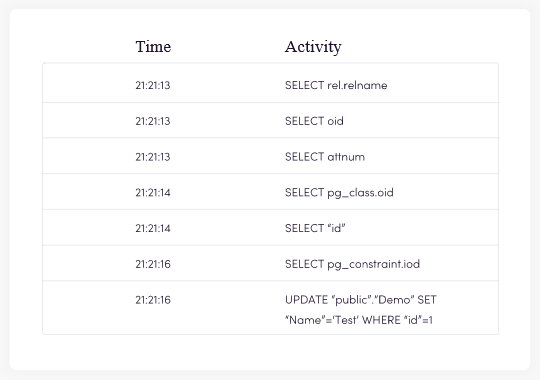
可見性
Get a complete audit trail of user activity, including all executed queries. All audit logs are tied to user accounts and devices and can be exported to your SIEM or other monitoring tools for additional contextual data.

即時安全
Provide granular, role-based access, monitoring all developer activity, and terminate sessions in real-time based on suspicious behavior.