Check Point® Software Technologies Ltd. (NASDAQ: CHKP), a leading provider of cyber-security solutions globally, has revealed that according to its latest Global Threat Impact Index, cryptomining malware affected 42% of organizations worldwide during February 2018.
Check Point’s researchers discovered three different variants of cryptomining malware in the February report of the Top 10 Most Prevalent Malware Ranking. While Coinhive maintained first place by affecting one-in-five organizations around the globe, Cryptoloot rose to second place after more than doubling its global impact from 7% in January to 16% in February. The Rig Exploit Kit followed closely behind in third place, with a global impact of 15% of all organizations.
Maya Horowitz, Threat Intelligence Group Manager at Check Point at Check Point commented: “Over the past four months, cryptomining malware has continued growing in prevalence. This persistent threat not only slows down PCs and servers, but once those agents have penetrated networks, they can also be used to carry out other malicious acts. Therefore, it is more important than ever for enterprises to employ a multi-layered cybersecurity strategy that protects against both established malware families and brand new threats.”
February’s 2018’s Top 3 ‘Most Wanted’ Malware:
*The arrows relate to the change in rank compared to the previous month.
- ↔ Coinhive – Crypto-Miner designed to perform online mining of Monero cryptocurrency when a user visits a web page without the user’s knowledge or approval
- ↑ Cryptoloot – Crypto-Miner that uses the victim’s CPU or GPU power and existing resources to add transactions to the blockchain and releasing new currency.
- ↔ Rig ek – Rig delivers Exploits for Flash, Java, Silverlight and Internet Explorer.
Triada, a modular Backdoor for Android, was the most popular malware used to attack organizations’ mobile estates followed by the Lokibot and Hiddad.
February’s Top 3 ‘Most Wanted’ mobile malware:
- Triada – Modular Backdoor for Android which grants superuser privileges to downloaded malware.
- Lokibot – Android banking Trojan and info-stealer, which can also turn into a ransomware that locks the phone.
- Hiddad– Android malware which repackages legitimate apps then releases them to a third-party store.
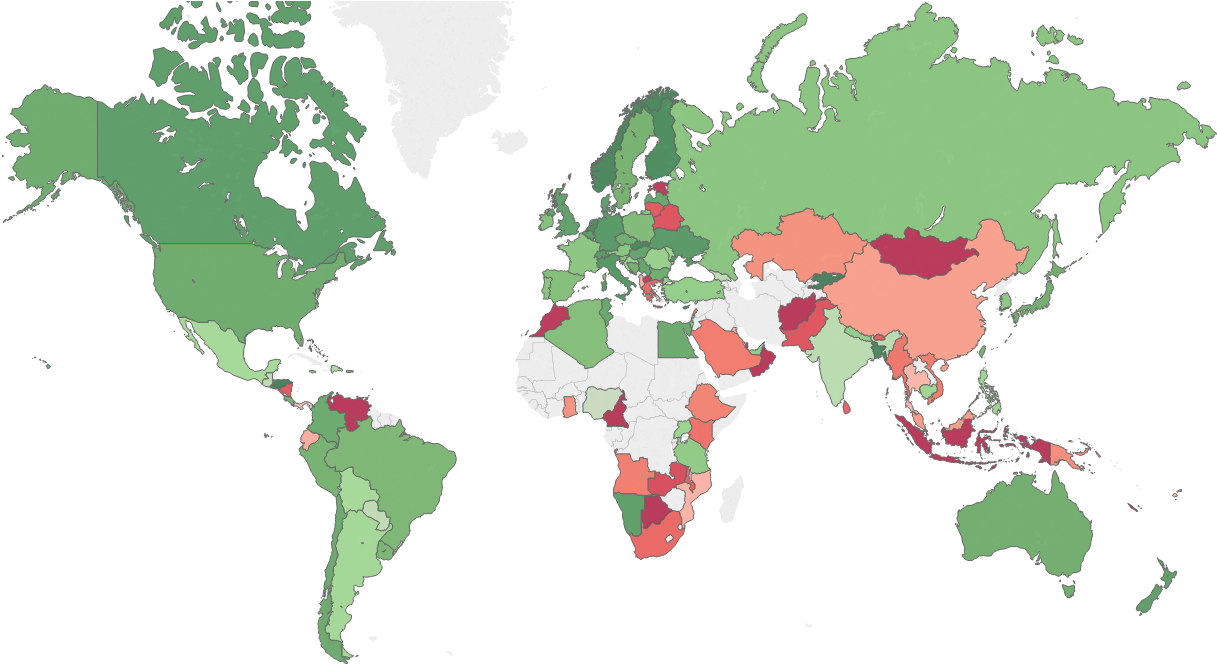
The map below displays the risk index globally (green – low risk, red- high risk, grey – insufficient data), demonstrating the main risk areas and malware hot-spots around the world.
Check Point’s Global Threat Impact Index and its ThreatCloud AI Map is powered by Check Point’s ThreatCloud AI intelligence, the largest collaborative network to fight cybercrime which delivers threat data and attack trends from a global network of threat sensors. The ThreatCloud AI database holds over 250 million addresses analyzed for bot discovery, more than 11 million malware signatures and over 5.5 million infected websites, and identifies millions of malware types daily.
* The complete list of the top 10 malware families in February can be found on the Check Point Blog: https://blog.checkpoint.com/2018/03/12/februarys-wanted-malware-cryptomining-malware-digs-deeper-enterprises-computing-resources/
Check Point’s Threat Prevention Resources are available at: /threat-prevention-resources/index.html
Follow Check Point via:
Twitter: https://www.twitter.com/checkpointsw
Facebook: https://www.facebook.com/checkpointsoftware
Blog: https://blog.checkpoint.com
YouTube: https://www.youtube.com/user/CPGlobal
LinkedIn: https://www.linkedin.com/company/check-point-software-technologies







