Streamline Infrastructure Security with Smart, Non-Disruptive Automation
Close exposures across infrastructure with validated remediation that protects uptime and keeps the business running smoothly.
Ensure Consistent, Validated, and Confident Security Actions
Close security gaps without risking uptime. Check Point validates every remediation before enforcement, giving infrastructure teams confidence to harden environments, reduce vulnerabilities, and keep operations resilient.
- Safe Remediation Across Environments Validate every configuration change, IPS activation, or policy update before enforcement, ensuring uptime and operational integrity.
- Maintain Secure, Consistent Configurations Automatically Continuously monitor and correct configuration drifts across network, endpoint, and cloud environments to maintain a secure baseline.
- Cross-Stack Orchestration and Control Simplify remediation execution across network, endpoint, and cloud. Check Point Exposure Management validates every change and automates enforcement safely – ensuring consistent controls, operational stability, and zero disruption.

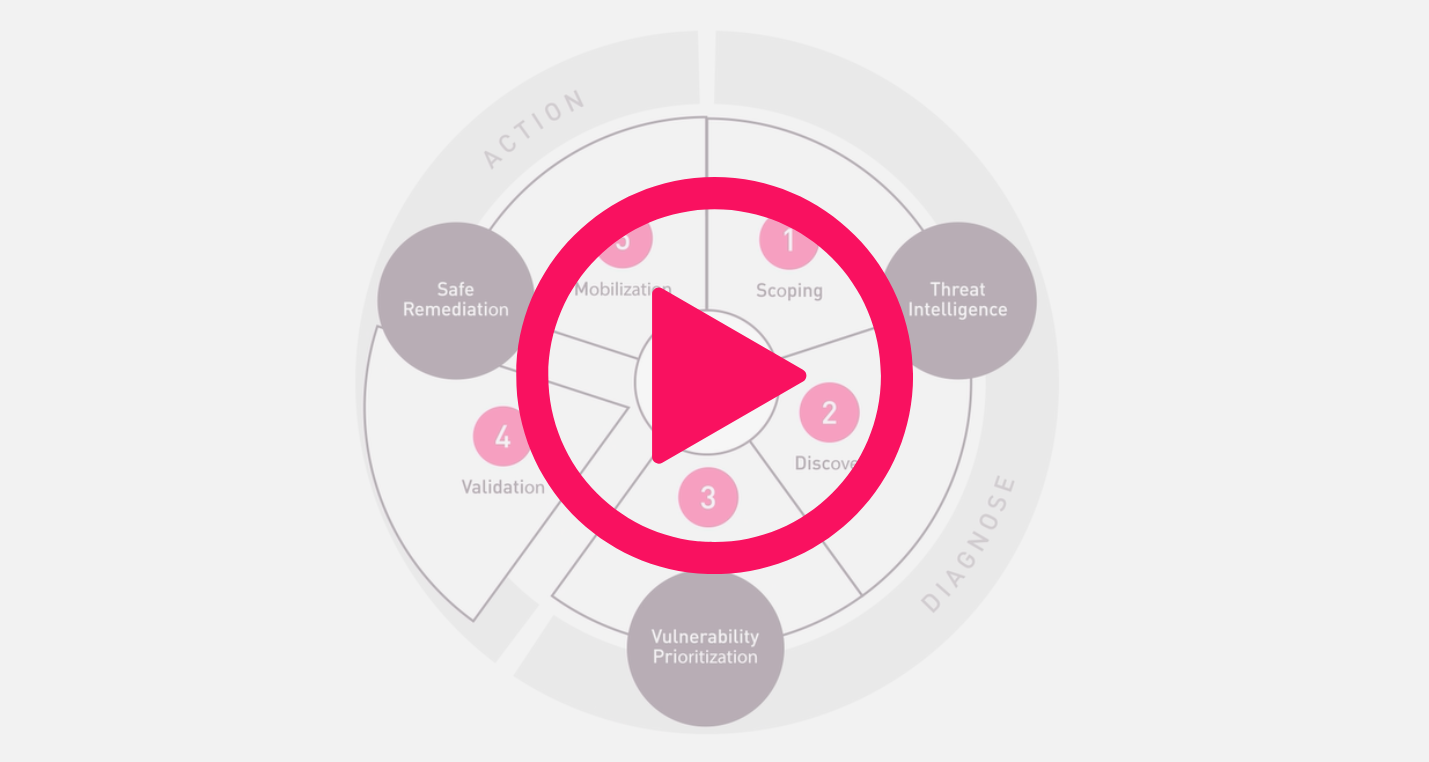
Check Point Exposure Management
We deliver the only unified solution that covers the full Continuous Threat Exposure Management (CTEM) framework, from intelligence and discovery through prioritization and safe remediation. Our open-garden approach is built for AI-era attacks and addressing exposure across complex, multi-team environments.
Validated by Infrastructure Leaders Worldwide
A Unified Solution Covering the Full CTEM cycle: Intelligence-led, Remediation-driven
Learn More About Securing Infrastructure

Threat Exposure Management Solution Brief
Proactively assess and safely remediate exposures
Exposure Management Playbook
This is the guide for staying ahead of threats without slowing the business down.